If you do not see a service listed here simply ask
Penetration Testing & General Audit
Penetration testing is the process by which the security of your computer infrastructure is examined and tested. Our examination is done in the same manner as if a malicious entity would attempt upon your organization. There are three levels of this type of testing:
a) External - attempts are made to penetrate the perimeter of your infrastructure and establish lateral movement through any means necessary. The methods are shared with you at the end when we present our report.
b) Internal Penetration - we place ourselves in your organization unbeknownst to your employees. Through various methods we blend in an attempt to infect and exfiltrate data from your organization. In this scenario you will know that we are there but the purpose of our presence is known only to you
c) Audit - A full analysis is done of your organization at the most granular level. Application usage, permissions, security (Systems Administration level), as well as network setup.
We personally believe all of the above should be done in one package, why?
Its not because we charge more, its actually one set fee.
No, the reason it should be done all at once is because you need to know what is going on because most likely - you do not
Most organizations charge quite a premium for such services. We believe that the cost should fit your organization, a small to mid-size does not have thousands of dollars laying around. We work with you as partners because your data is the bedrock of your business, it must be protected. So let us unleash the efficiency you have but just didn't realize it

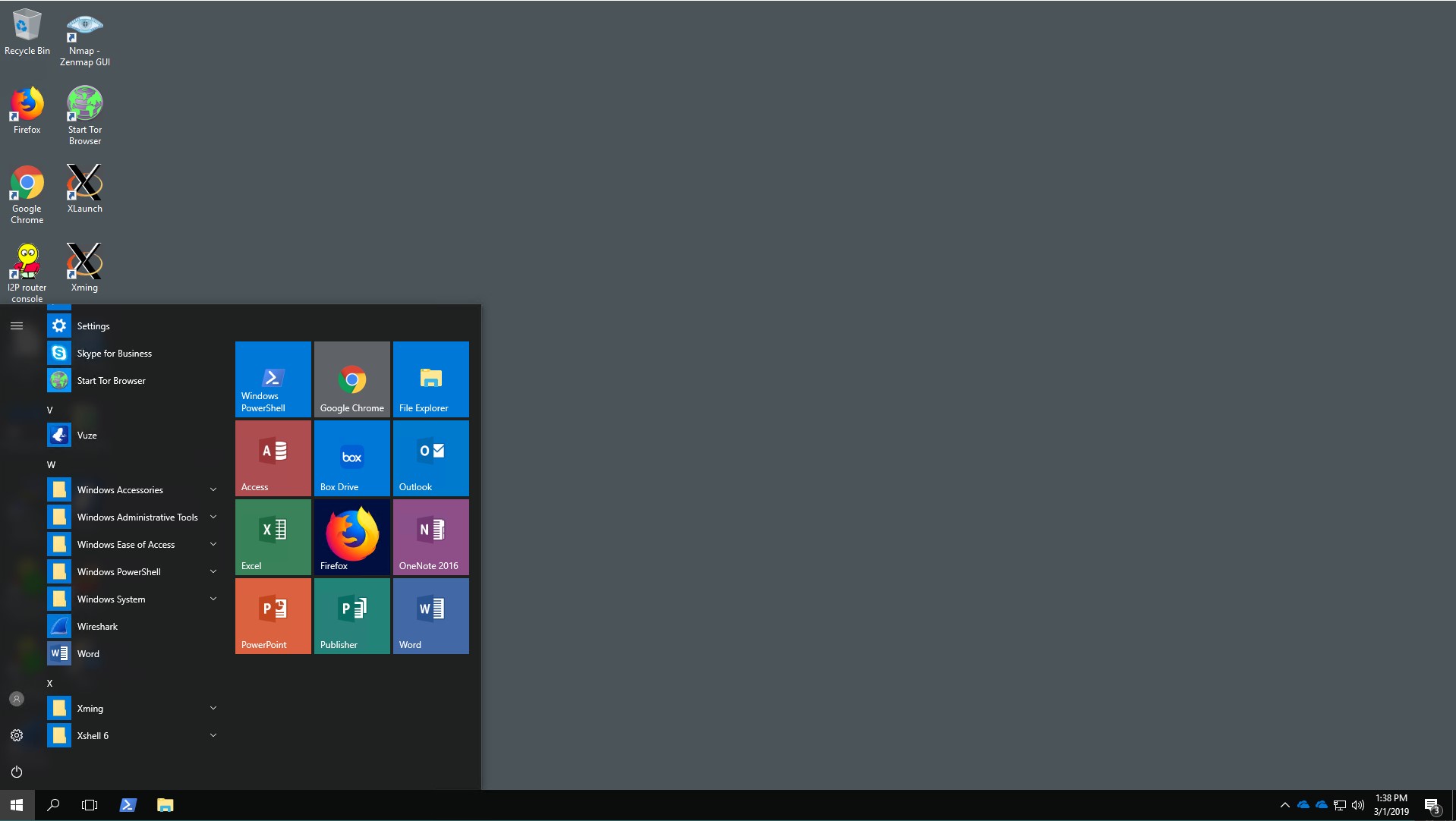
Secure Eco System
Cybercrypto offers a hosted secure ecosystem. Your productivity is not hindered but all data in your organization is locked down and behavior is analyzed in a real-time manner. We offer both a Linux based eco-system and a Windows based eco-system. Your mobile devices are incorporated into the system. Employees have access to the same applications as they would have in your office under normal circumstances.
Messaging is secured and end to end encryption is used to protect your communications. A designated administrator is then given access to analyst data which shows behavior on your network as well as all connected websites. Nothing happens on that network without you knowing about it. Both Cybercrypto and yourself receive alerts as to everything going in and out. An example of why this is necessary, there should be no reason that the maintenance man is copying data from the Human Resources department onto his USB drive. We monitor your systems for your day to day support issues as well as detecting anomalies that may occur
This type of service requires an audit of your environment as well as your data. It is done in a modular fashion so as not to interrupt workflow. We catch infections before they do damage and prevent your data from leaving the building.
We also streamline your applications and become your hosted provider where your apps and data live in a happy walled in garden.
Want to see what it looks like?
The snapshot below is an example, it looks just like any other desktop, but its remote, modular, powerful, and you can work anywhere.

Website and Database Management Design
Cybercrypto also will design your website for you in conjunction with a secure eco-system. We focus on a particular level of development, in that we do intranets, public facing websites that interface to your business, as well as database application design. Data is the bedrock of your business and you need to be able to access it from wherever you are. We will create a website that is not only functional but is application driven, in that it becomes a tool for your business.
Any business can create a website, do you want a pretty sign post on the road or a factory that is producing something you can use. A lot of things go into this, but the point is – functionality is king. An example:
- A medical clinic where the patient logs into your site, enters their information and their records are available to them on demand
- The client makes an appointment on your website, your people are notified, and it goes directly into your Outlook calendar along with details without leaking credentials
- A client for a law firm can check on the status of their case and leave secure messages for their counsel.
Everything starts at the data level. Build around this and you will have something functional that works for you. Start with a public facing website, make it pretty and start the backend to make it functional. Once the database is setup correctly there is not one thing you cannot do.
Think outside the box or let us build one for you.
Reputation Management
Your web presence is essential to who you are. This is a blessing and a curse. The good it brings is obvious, plus it allows people to make some level of judgement to help them in procuring the service they wish or what goods they want to buy. From restaurants, doctors, to lawyers – reviews can for the most part be a good thing.
There is like most things on the internet a dark side. Negative reviews are brutal, its one thing if they were true but we have seen a surge in reviews that are meant to cause a business harm. Removing such things can be quite the task because even though most places will tell you to flag the review, in our experience we have seen many providers simply ignore you.
We bared witness to one attorney that got into a conflict with a client, and at the end of this conflict what we proved was the client posted several negative reviews under different names. When the attorney flagged the reviews with google and said that he never had a client with this name, his statements were simply ignored.
Such things are powerful because they can literally cripple you and worse due to laws passed you have little recourse, who wants to file a defamation lawsuit?
We also recognized that some people need their reputation sanitized, this is a lengthy process and not for the faint of heart as takes a lot of time and a lot of content, but we can get that negative stuff pushed down.
Reputation management is not done quickly and as most things requires discipline and patience. Each case is very different, and we tailor out attack per the specifications of the scenario. If you have bones that must be burned online, and your reputation sanitized, talk to us. We do not judge.
Forensics for small to mid-size companies
Cybercrypto has a proven track record of not only retrieving data for forensic analysis but we have worked with several law firms where we extract the data, analyze, and it prepare for submission to the court.
We will also be able to perform forensic analysis if you have suffered a breach or have been the victim of hacking or data theft. When we receive word that something has happened we come in immediately secure the environment and extract as much logs as possible to reconstruct what happened and attempt to discover who caused it.
Forensic analysis is not constrained or exclusive to computer but encompasses any digital device. We can take it, secure it, and extract the data.
This service does not just apply to law firms. It applies to any company who has suffered an attack or data theft and wants to know what happened.
Data theft, malware attack, and intrusion detection. When the incident has occurred, everything done post occurrence is forensics. We will be able to take it apart and tell you the who, what, where, and possibly even the why.
If you have been a victim of a malicious attack we can help you put the pieces together and then solidify yourself so that it doesn't happen again.

Remote Work Setup and Infrastructure
Shatter the chains that bind you and rise up from the ground
We live in strange times, pandemics (Covid-19), illness, and all-around odd behavior. A remote work force is no longer a niche item. There is no reason whether you are a medical clinic, law firm, or any other business to not have some level of remote work. If you are a medical clinic, your doctors given the proper setup along with your infrastructure can treat patients from afar. Attorneys need to see their clients and in Florida some people are too sick to travel, there is no reason why you should not be able to video conference with your client as well as exchange documents. There is no reason whatsoever that any of your workers when at home cannot commit to the same functions that they act on in the office or some deviation of their day to day so that they are still productive at home.
Too often small business views this as something scary, this is simply is not true. Remote work is not only possible, but it is affordable because often the tools are already present in the very apps you are using. After a site audit we can configure a remote system for some of your workers that not only will increase your productivity but also make your life easier.