Malware and Behavior Analysis – Series Two
Section One:
Overview
Why do people attempt to infect a network? Why do people attempt to move data? Your information can be monetized. As most people are not aware of the insidious nature of those who lurk underground, they do no give much thought to their data and what can be done with it. If you lurk in the sublayers of the internet or you are tasked with retrieving information from a target you need a mechanism to deliver this information. Ransomware is a savage method to which there is no art and it will bring you nothing. A Trojan is the order of the day.
A Trojan is a malware that is for the most part disguised as some sort of normal software. Delivery of a trojan can involve just about anything, usually some level of social engineering is employed to obtain activation. What do they do? Anything along the lines of:
- Deleting data
- Blocking data
- Modifying data
- Disrupting the network
- Copying data *****This is where the money is
A remote access trojan is exactly as it sounds, a piece of malware that allows for a backdoor which will provide administrative control over the target. Remote Access Trojans otherwise knows as “RATs” like most trojans are delivered via social engineering such as phishing. Once the target is compromised, data is sent back to the command and control center. What does that mean? It is exactly as it sounds.
Remote Access Trojans enable administrative control, making it possible for the operator behind the command and control center to just about anything on the target, including but not excluding:
- Monitoring user behavior
- Accessing your confidential information
- Screenshots
- Distributing malware
- Copying data
I personally find Trojans to be far more interesting, there is no finesse in ransomware, in my opinion it is brutish and seeks destruction without elegance. A good Trojan will supply the writer what he needs and achieve some level of purpose that completes his/her end goal. For the most part, if they are truly any good, it is to get your data. With that being said, let’s look at how Remcos spawn.
Remcos has been circulating in hacking forums since the second half of 2016. From that point it has been updated with new features (just like regular software). It is a commercial Remote Access Trojan and usually goes from anywhere between $58 to $389. We take a more granular look at how this Trojan works from two levels – the malware itself and what it does to the computer via the logs.
Section Two:
Analysis - Sandbox
As in all analysis that we do, there is a lot see here. We view the malware from our sandbox and analyze the findings to view what exactly it was doing focusing on the more interesting parts
Item One:
An unhook function is attempted to modify the windows functions monitored by the sandbox
Item Two:
The sandbox performs a static analysis of the malware. Some of the strings extracted stand out:
CompanyName
Breaking-Security.net
FileDescription
REMCOS Remote Control & Surveillance
FileVersion
1.7.0.0
LegalCopyright
BreakingSecurity.net
LegalTrademarks
BreakingSecurity.net
ProductName
REMCOS Remote Control & Surveillance Software
ProductVersion
VarFileInfo
Translation
Anything that says BreakingSecuirty and Surveillance most likely is a bad thing.
Item Three:
In the behavioral analysis section, we get a true granular view of Remco at work. Here we see threads being suspended. Those threads belong to the sandbox and how it monitors the windows system
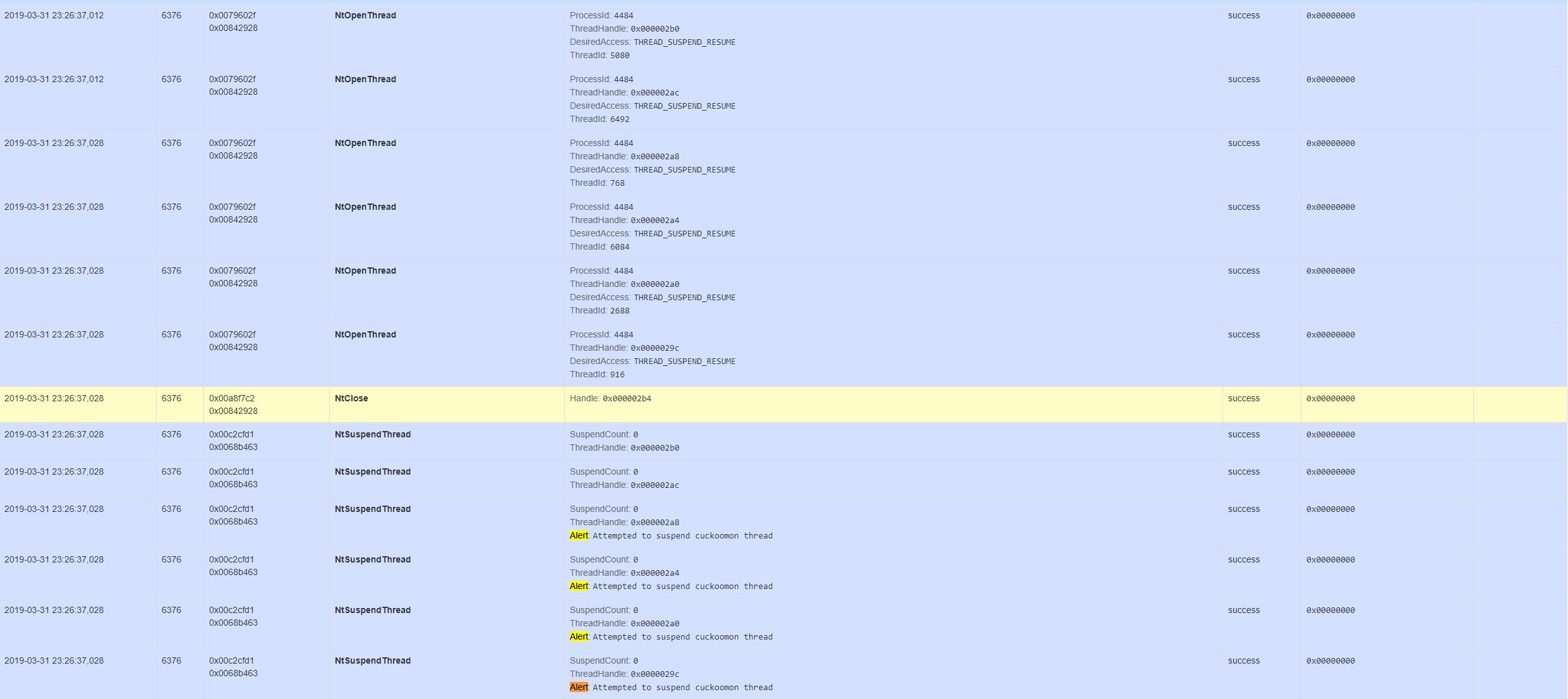
Item Four:
A mutex is short for mutual exclusion object. It is a program object that is created so that multiple programs thread can take turns sharing the resources to access to a file, however not simultaneously. Mutexes are important as they show you what is going with a program. When a program begins the mutex is created with a name that is unique, after this stage, any thread that needs the resource must lock the mutex from other threads while it is using the resource. With that knowledge in hand I recommend looking deeply at the behavior analysis, which is located at the link at the very end of this article, it always makes for interesting reading at the forensic level. The mutex in this case with Remco is listed below –
REMCOS_C&C_MUTEX
Local\SM0:4484:168:WilStaging_02
Local\SM0:4484:64:WilError_01
Local\MSCTF.Asm.MutexDefault1
CicLoadWinStaWinSta0
Local\MSCTF.CtfMonitorInstMutexDefault1
If one understands nothing else with above, the fact that a mutex says C&C is quite telling.
Section Three:
The logs have a story to tell you
Your logs tell a story, they enable you to reconstruct what has occurred, and if you are clever enough it can help you stop a malady while it is going on. We are not so interested in after the fire, but what leads up to the fire.
Item One:
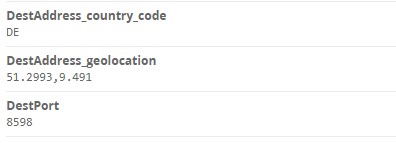
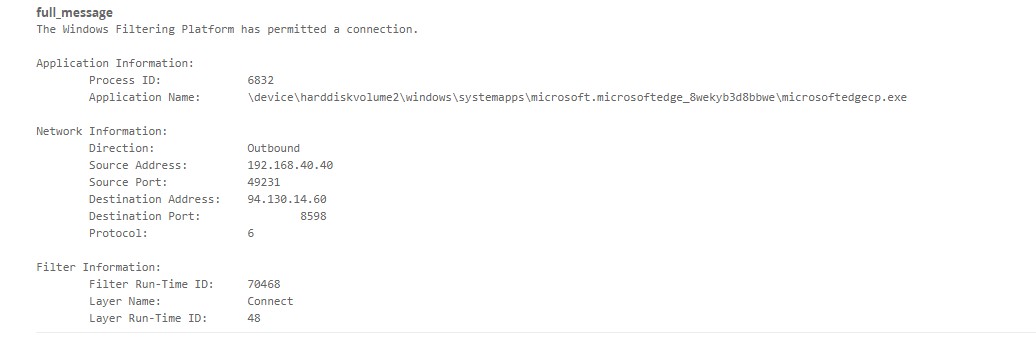
A user has accessed a webpage with an ip address of 94.130.14.60 with a port of 8598. We capture geolocation in our system, this ip is in Germany. This is an unusual port and triggers an alert.
Item Two:
An object by the name of “turbotax.exe” has triggered “An attempt was made to access an object”. We now have two warning signs here that have been sent to the system operator. These alerts alone are enough to prompt the operator to pay a visit to the workstation to see what is going.

Item Three:
Here we see odd behavior. “turbotax.exe” after being downloaded is launched with the parent process of explorer.exe. In itself this would be the case for any program however there is something odd here. The parent commandline for explorer.exe contains a “/NOUACCHECK” at the very end. When explorer is executed with the “/NOUACCHECK” switch, explorer is launched conventionally inheriting any elevated states from the process that launch it. While not a glaring red flag, this is something worth investigating as to why something would install itself with such a suffix attached.
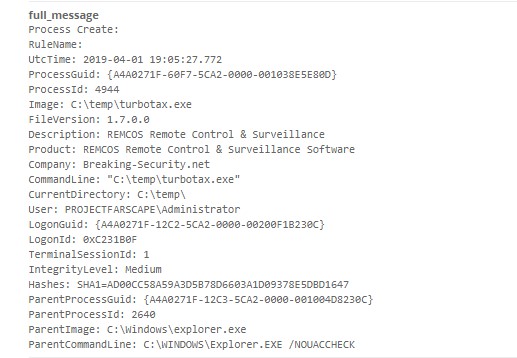
Much like the sandbox analysis we see in the logs “Breaking-Security.net” as well as the REMCOS description in the Product field. We also look for alerts produced from images which are not common in the local network. A foreign executable launching with an integritylevel of medium creates an alert which the operator needs to investigate
Conclusion:
In future postings I will delve into complete scope of damage that these Trojans do, that however is not the point of what we want to explore. One can find a plethora of sites that will instruct you on the damage done by any type of malware (Do not fear we will do that too – but that will be a separate series) Our interest is identifying patient zero and isolating it before the disease spreads. If you catch it, then the damage is contained.
Remember, persistence is everything. When the attacker has hooked themselves into your system, they will wait, move the data out, at most you will see a process spiking your CPU while you are left with the cliché of “WTF!!!.” Find patient zero, kill the disease before it spreads.